In the era of digitalization, computer networks play an extremely important role, connecting billions of devices worldwide. When learning about networking, I realized that TCP/IP is the foundational protocol that determines how data is transmitted between devices, from personal computers and smartphones to servers on the Internet.
Understanding TCP/IP not only helps us understand how data “travels” from one device to another, but also opens up opportunities to explore many other aspects of computer networks, from network programming and network administration to security and performance optimization. In this article, I will explore the TCP/IP model with you, from its concepts and layer structure to how data is transmitted through each layer and its real-world applications. This helps provide a comprehensive picture of how the Internet operates every day, as well as the foundation for developing network applications in the future.
1. The Concept of TCP/IP and Its Historical Development
TCP/IP stands for Transmission Control Protocol / Internet Protocol. It is a standard protocol suite that enables devices on a network to connect and exchange data with one another. In other words, TCP/IP is the “common language” that allows all devices to understand and communicate with each other, and it serves as the fundamental foundation of the modern Internet.
Historically, TCP/IP was developed from the ARPANET project in the late 1960s and early 1970s, with the goal of building a reliable network to connect computers used by the military and research institutions. In 1983, TCP/IP officially became the standard protocol for Internet connectivity and has since been widely adopted worldwide, ushering in the era of global networking.
Compared to the seven-layer OSI model, TCP/IP is more compact and practical, making it better suited for implementation on the Internet. While the OSI model is largely theoretical and academic, TCP/IP focuses on real-world communication between devices, enabling data to be transmitted quickly and efficiently. Thanks to its flexibility and scalability, TCP/IP has become the basic standard upon which most modern network systems rely, from enterprise networks to widely used Internet services in everyday life.
2. Structure of the TCP/IP Model
The TCP/IP model is designed with four main layers, each responsible for a specific function. These layers work closely together to ensure that data from user applications is transmitted safely, efficiently, and accurately to its final destination.
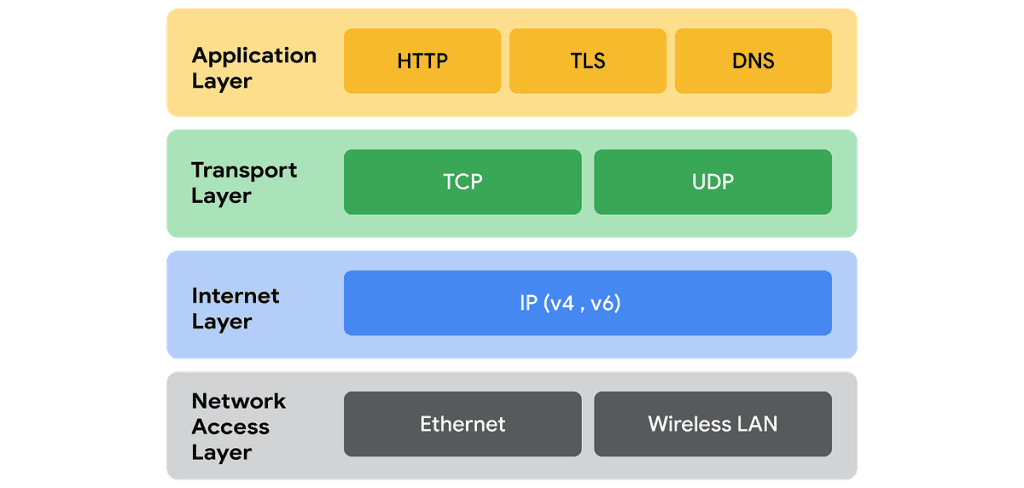
2.1. Application Layer
The Application layer provides a direct interface between users and the network, allowing applications such as web browsers, email clients, and chat software to send and receive data. This is the layer where data “begins its journey” from user applications, and it is also responsible for handling user requests and formatting data appropriately before passing it down to the lower layers.
Key protocols at this layer include:
- HTTP/HTTPS: Web browsing and secure information exchange between browsers and servers (HTTPS).
- FTP: File transfer between computers and servers, supporting data uploads and downloads.
- SMTP/POP3/IMAP: Sending and receiving email, ensuring messages are delivered to the correct mailbox and can be accessed from multiple devices.
- DNS: Converting domain names into IP addresses, enabling data to be routed accurately to the destination server.
For example, when you access a website, the browser sends an HTTP request to the server. The data is then encapsulated and passed down through the lower layers for routing and verification, reaches the server, and receives a response. Thanks to the Application layer, we can under-
2.2. Transport Layer
The Transport layer is responsible for ensuring that data is transmitted reliably and accurately between two devices on a network. This layer determines how data is segmented, error-checked, and arranged in the correct order before it is delivered to the user’s application.
The two most important protocols at this layer are:
- TCP (Transmission Control Protocol):
A connection-oriented protocol that establishes a “session” between two devices before data transmission.
It ensures that data arrives in the correct order without loss or duplication, making it suitable for file transfers, email, and web communication. - UDP (User Datagram Protocol):
A connectionless protocol that sends data quickly but does not guarantee complete or reliable delivery.
It is commonly used for applications that require high speed, such as video streaming, online gaming, or VoIP, where the loss of some packets does not significantly affect the user experience.
The Transport layer acts as a critical bridge between applications and the underlying network infrastructure.

2.3. Internet Layer
The Internet layer is responsible for routing and forwarding data packets between devices on a network, ensuring that data travels accurately from the source to the destination, even when passing through multiple intermediate networks. This layer is in charge of “choosing the path” for data, much like the navigation system of the Internet.
The main protocols at this layer include:
- IP (Internet Protocol): Provides IP addressing for devices, including both IPv4 and IPv6, in order to route data to the correct destination device.
- ICMP (Internet Control Message Protocol): Used to send network error messages or to test connectivity, such as with the ping command.
When a data packet is sent, IP encapsulates the source and destination address information, enabling the data to “take the correct route” through routers. Tools such as ping or traceroute illustrate how data is transmitted through multiple routers, demonstrating how routing and connectivity checks operate.
Thanks to the Internet layer, different networks can interconnect continuously and flexibly, even when they use different infrastructures. This layer also helps manage network traffic efficiently.
2.4. Network Access / Link Layer
The Network Access or Link layer is responsible for transmitting data over the physical network, from Ethernet cables and Wi-Fi signals to devices such as switches and routers. This is the layer closest to the hardware, ensuring that data is sent correctly over the physical medium and reaches the appropriate device within the local network.
Common protocols at this layer include:
- Ethernet: A widely used wired LAN networking technology.
- Wi-Fi: A wireless networking technology for mobile devices and computers.
- ARP (Address Resolution Protocol): Resolves a device’s MAC address from its IP address.
At this layer, data is encapsulated into frames, along with MAC address information to identify devices on the local network. For example, when a PC sends data to a router, the Network Access layer ensures that the frame is transmitted via a cable or Wi-Fi signal and delivered to the correct device.đến đúng thiết bị đích, đồng thời kiểm soát lỗi truyền tải cơ bản để duy trì sự ổn định của mạng.
3. The Data Transmission Process in TCP/IP
Data in the TCP/IP model goes through a sequence of orderly steps, from the moment it is generated by an application until it reaches the destination device, ensuring reliability and accuracy.
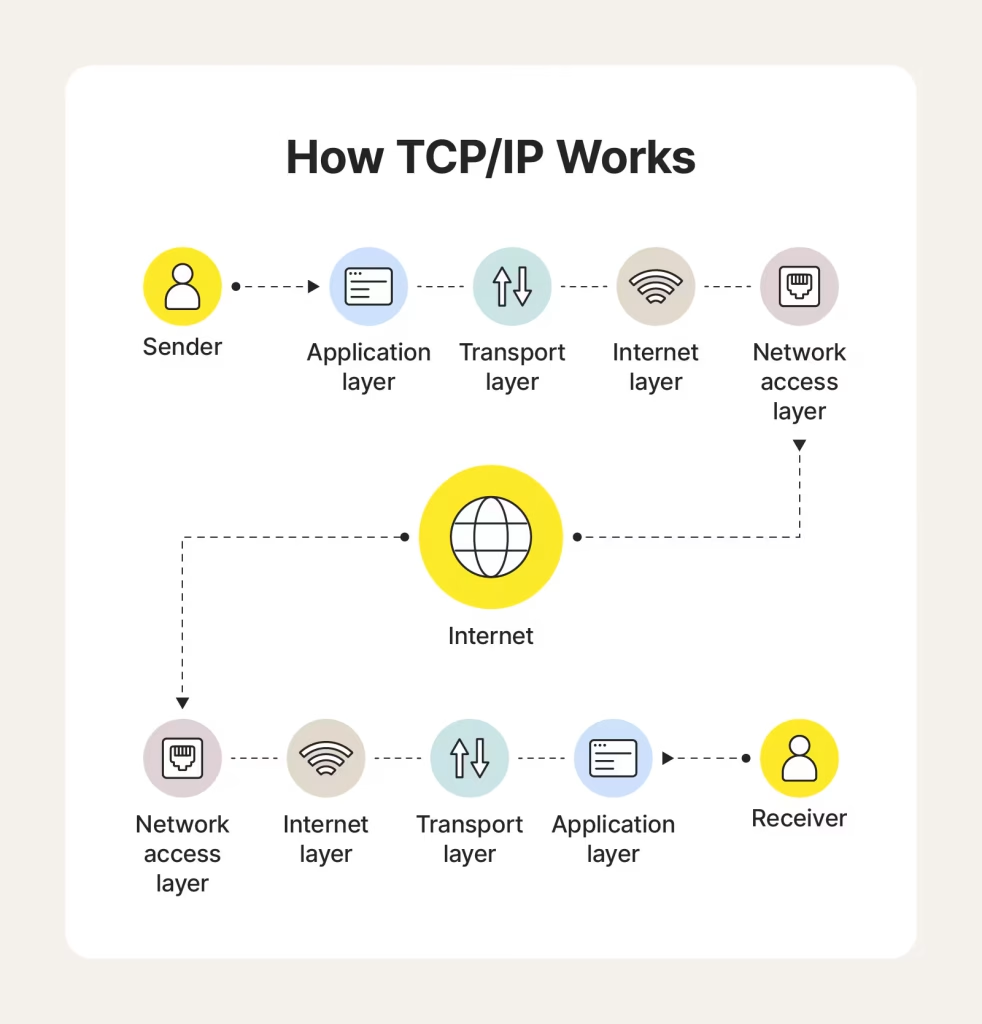
- Application Layer: Data is generated by the application, such as an HTTP request when browsing the web or the content of an email when sending a message.
- Transport Layer: The data is divided into segments (TCP) or datagrams (UDP), and port information is added to identify the receiving application.
- Internet Layer: The segments/datagrams are encapsulated into packets, along with source and destination IP addresses, which determine the path the data takes across the network.
- Network Access Layer: The packets are encapsulated into frames, combined with MAC addresses, and transmitted over the physical network, such as Ethernet cables or Wi-Fi signals, to the destination device.
This process is called encapsulation, meaning that data is “wrapped” layer by layer before being transmitted. When the data reaches its destination, the decapsulation process takes place: each layer unwraps the data so that the final application can correctly read and process the information.
Illustrative example: When you send an email from Gmail, the message content goes through the entire process – from data segmentation, IP addressing, and frame encapsulation to reaching Google’s servers and then being forwarded to the recipient – ensuring that the email is delivered quickly and accurately.
4. Advantages and Limitations of TCP/IP
Advantages of TCP/IP:
- It is an open and widely adopted standard, easy to deploy across various platforms, from personal computers and smartphones to large servers. This enables different systems to communicate with one another without barriers related to software or hardware.
- It supports internetworking, allowing the interconnection of multiple types of networks, from LANs and WANs to the global Internet, ensuring that data can traverse complex network environments.
- TCP provides reliability by segmenting data, performing error checking, and ensuring correct ordering, allowing applications to receive data accurately and completely.
Limitations of TCP/IP:
- Lack of built-in security: TCP/IP does not inherently encrypt data, so additional protocols such as SSL/TLS are required to protect sensitive information during transmission.
- Complex management in large networks: When deploying TCP/IP in large-scale networks, configuring routing, subnetting, and traffic management requires advanced knowledge and supporting tools.
- Bandwidth overhead in certain cases: Because TCP ensures reliability, it introduces additional overhead through acknowledgments and control mechanisms, which can reduce performance in applications that require high speed but are less sensitive to packet loss.
Despite some limitations, TCP/IP remains a solid foundation for the modern Internet. It lays the groundwork for advanced security and enterprise networking solutions such as HTTPS, VPNs, and secure data transmission systems, while also enabling the Internet to be flexible, scalable, and reliable. Thanks to TCP/IP, devices and applications around the world can communicate seamlessly, supporting the continuous growth of online services, cloud applications, and today’s Internet of Things (IoT).
5. Practical Applications of TCP/IP
TCP/IP is the foundation of the Internet and modern networks, playing a crucial role in most online services that we use every day. Thanks to its layered architecture and scalability, TCP/IP supports a wide range of applications, from basic communication to complex systems.
Some typical applications include:
- Web, email, video/audio streaming: Reliable data transmission over the Internet, ensuring that users receive information completely and in the correct order.
- VoIP, online chat: Real-time voice and messaging transmission, using a combination of TCP and UDP depending on requirements for speed and reliability.
- Cloud computing and IoT: Connecting devices, servers, and cloud services, enabling continuous and synchronized data exchange across multiple platforms.
For example, a simple TCP client–server model (as presented in the Transport section) illustrates how data is transmitted reliably between two devices. In practice, all Internet services are based on similar mechanisms, differing mainly in scale, additional protocols, and accompanying security features. Thanks to TCP/IP, applications and services can operate seamlessly, stably, and at scale, from personal connections to enterprise networks and the global Internet.
6. Comparison between TCP/IP and the OSI Model
The TCP/IP model and the OSI model both use a layered approach to organize how data is transmitted across networks, but they differ in terms of the number of layers, objectives, practicality, and applications:el and the OSI model both use a layered approach to organize how data is trans-
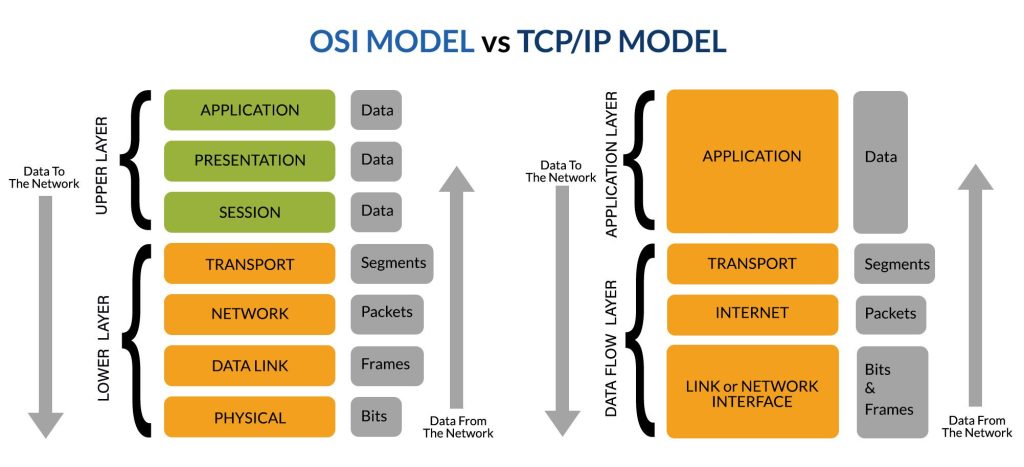
- Number of layers and layer division
- OSI: Consists of seven clearly defined layers – Physical, Data Link, Network, Transport, Session, Presentation, and Application. Each layer has a distinct function, which helps separate responsibilities and makes theoretical study easier.
- TCP/IP: Has only four layers – Network Access, Internet, Transport, and Application. TCP/IP combines several OSI layers (for example, Session and Presentation) into the Application layer, simplifying the architecture and making it easier to implement in practice.
- Design objectives
- OSI: Focuses on providing a theoretical description of how devices communicate, serving as a reference model for developing and comparing network protocols.
- TCP/IP: Aims at practical implementation, ensuring that data is transmitted accurately, reliably, and compatibly between devices on the Internet.
- Practicality and popularity
- OSI: Primarily academic in nature and rarely used directly in network deployment; it mainly serves as a conceptual reference.
- TCP/IP: The practical standard of today’s Internet, widely applied in LANs, WANs, enterprise networks, and online services.
- Data handling approach
- OSI: Each layer defines specific functions and rules for data encapsulation, decapsulation, and error checking.
- TCP/IP: Focuses on efficient data transmission; data is encapsulated, routed, and error-controlled, but some functions are combined to simplify design and accelerate deployment.
- Scalability and compatibility
- OSI: Strong in theory, but implementing the full seven-layer model is complex and less flexible.
- TCP/IP: Flexible, easy to scale, and compatible with many types of networks and devices, enabling the rapid and synchronized growth of the Internet worldwide.
In summary, TCP/IP is a more practical, streamlined, and widely adopted version compared to the OSI model. While still based on layered principles, it is optimized for real-world network implementation, enabling reliable data transmission and efficient operation of Internet services.
7. Conclusion
The TCP/IP model is a fundamental foundation of modern computer networks and the Internet, enabling data to be transmitted reliably, accurately, and flexibly. Its four main layers – Application, Transport, Internet, and Network Access – work closely together to ensure that data travels from applications to its final destination while maintaining effective error control and routing.
The TCP protocol provides reliability, while UDP optimizes speed for real-time applications. The Internet layer is responsible for routing data between different networks, and the Network Access layer ensures data transmission over the physical medium. TCP/IP also offers an open, easy-to-deploy framework that is compatible with a wide variety of networks.
Compared to the OSI model, TCP/IP is more compact and practical, with a strong focus on real-world network implementation. As a result, knowledge of TCP/IP is essential for understanding how Internet services – from the web and email to IoT – operate efficiently. In the future, a solid understanding of TCP/IP will remain a key prerequisite for researching new protocols and developing modern, secure networking solutions.
8. References
[1] W. Richard Stevens, TCP/IP Illustrated, Volume 1: The Protocols, 2nd ed. Boston: Addison-Wesley, 1994.
[2] Andrew S. Tanenbaum and David J. Wetherall, Computer Networks, 5th ed. Boston: Pearson, 2011.
[3] J. F. Kurose and K. W. Ross, Computer Networking: A Top-Down Approach, 8th ed. Boston: Pearson, 2021.
[4] Behrouz A. Forouzan, TCP/IP Protocol Suite, 4th ed. New York: McGraw-Hill, 2013.
[5] D. E. Comer, Internetworking with TCP/IP Volume One, 6th ed. Upper Saddle River, NJ: Prentice Hall, 2013.
[6] K. Fall and W. Stevens, TCP/IP Illustrated, Boston: Addison-Wesley, 2012.
[7] Wikipedia contributors, “TCP/IP,” Wikipedia, 2025. [Online]. Available: https://en.wikipedia.org/wiki/TCP/IP. [Accessed: Oct. 7, 2025].