In the online world, every time you enter a password, make a payment, or submit a form, your data embarks on a “journey” across multiple servers, routers, and network gateways. This raises an important question: who can read that information?
To ensure this journey is secure, SSL/TLS technology was created – acting as an intelligent encryption system that allows information to reach its destination without being stolen or altered.
In this article, you and I will explore how SSL/TLS works, understand how it protects users, and examine practical ways to deploy it for websites or applications. I believe that with a clear understanding, we will see that HTTPS is not just a “small padlock in the address bar,” but the foundation of digital trust.
1. What Is SSL/TLS?
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are security protocols designed to protect data during transmission between a browser (client) and a server. They ensure that information – such as passwords, credit card numbers, or message content – is not eavesdropped on, altered, or spoofed while traveling across the Internet.
In essence, SSL/TLS creates an encrypted communication channel in which all data is “wrapped” into a form that is unreadable to anyone other than the legitimate sender and receiver. Even if someone intercepts the data in transit, all they will see are meaningless strings of characters.
The three core objectives of SSL/TLS are:
- Confidentiality:
Data is encrypted using algorithms such as AES, RSA, or ChaCha20, preventing outsiders from reading the actual content. - Integrity:
The protocol uses verification mechanisms (MAC – Message Authentication Code) to ensure that data is not modified during transmission. If any alteration occurs, the system detects it and terminates the connection. - Authentication:
SSL/TLS uses digital certificates to verify the identity of the server, ensuring that users are communicating with the legitimate website rather than a fake one.
Historically, TLS is the successor to SSL, developed to improve security and performance. After SSL 3.0 was found to have multiple vulnerabilities, TLS 1.0 was introduced and gradually replaced SSL entirely. Today, TLS 1.3 (defined in RFC 8446) is the latest version, offering a faster handshake process, eliminating weak algorithms, and strengthening protection against man-in-the-middle (MITM) attacks.
In short, SSL/TLS is the “security shield” of the modern Internet, making online transactions, logins, and information exchanges trustworthy.

2. How SSL/TLS Works
At a high level, SSL/TLS operates in two main phases: the handshake process and secure data transmission (encrypted communication).
- The handshake phase allows both parties to agree on encryption algorithms, authenticate each other, and generate a session key.
- The next phase uses this session key to encrypt all transmitted data, ensuring security and high performance.
Handshake Process (Overview):
- ClientHello: The browser (client) sends information about the TLS version, a list of supported encryption algorithms (cipher suites), and a random value (nonce) to initiate the session.
- ServerHello: The server responds by selecting an appropriate algorithm, sending its own nonce, and providing a digital certificate (X.509) containing its public key so the client can verify its identity.
- Certificate verification: The client checks the certificate – verifying that it is issued by a trusted Certificate Authority (CA), is still valid, and matches the domain being accessed. If everything is valid, the process continues.
- Key exchange: Using methods such as ECDHE (Elliptic Curve Diffie-Hellman Ephemeral), both parties jointly generate a shared session key. Due to the mathematical properties of ECDH, even if an attacker intercepts the public keys, they cannot derive the secret key.
- Data encryption: Once the handshake is complete, data transmission begins using symmetric encryption algorithms (such as AES-GCM). This approach is fast and efficient, making it suitable for continuous data transfer.
TLS 1.3 – the latest version – has streamlined the handshake process to just 1–1.5 round trips, improving connection speed, eliminating weak algorithms, and reducing the risk of man-in-the-middle (MITM) attacks.
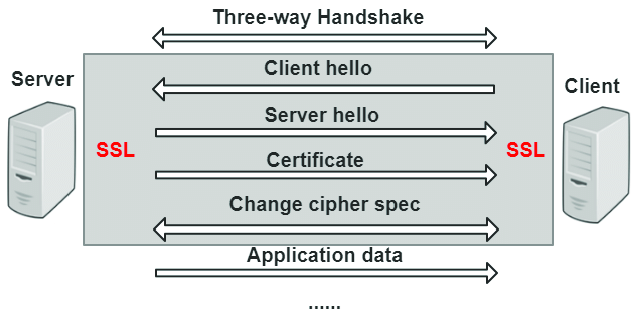
In summary, public/private keys are used during the authentication phase and the initial establishment of shared secrets, while the session key serves as a “temporary key” to encrypt all subsequent data – ensuring security while also providing optimal transmission performance.
3. Types of SSL/TLS Certificates
SSL/TLS certificates are categorized into different types based on their validation level and scope of coverage. Understanding each type helps you choose the certificate that best fits the needs, scale, and budget of a website.
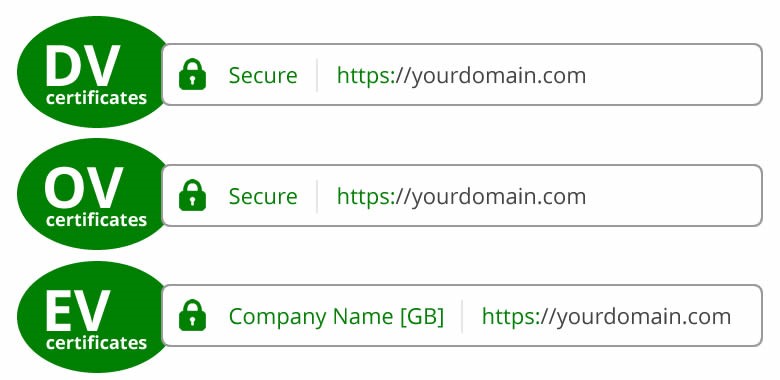
3.1 Classification by Validation Level
- DV – Domain Validation: This is the most basic type of certificate. The Certificate Authority (CA) only verifies that you own or control the domain name, typically via email confirmation or a DNS record. Issuance is very fast, often taking only a few minutes. It is suitable for personal blogs, small projects, or testing websites.
Example: Let’s Encrypt is a popular CA that provides free DV certificates and supports automatic renewal. - OV – Organization Validation: At this level, the CA not only verifies domain ownership but also validates the organization or business behind the website. The applicant must provide legal documents such as business registration or valid contact information.
This type is suitable for organizations, companies, or service websites that need to demonstrate a higher level of trust. - EV – Extended Validation: This is the certificate type with the strictest validation requirements. The CA conducts a thorough verification of the company’s identity, address, ownership, and legal status. In the past, browsers displayed the company name next to the padlock icon, but this visual indicator has since been simplified.
Nevertheless, EV certificates remain a top choice for banks, e-commerce platforms, and large enterprises that need to demonstrate maximum credibility.
3.2 Classification by Scope of Coverage
- Single Domain Certificate:
Protects a single domain name, for example:example.com.
Suitable for standalone websites or simple informational pages. - Wildcard Certificate:
Protects all first-level subdomains of a domain. For example,.kienthucmo.comcoversshop.kienthucmo.com,blog.kienthucmo.com, and so on.
This is very convenient for systems with multiple services or sub-applications under the same domain. - Multi-Domain (SAN) Certificate:
Allows multiple different domain names to be protected under a single certificate, for example: https://kienthucmo.com/,openbook.org,opentech.net. This is suitable for businesses or organizations that manage multiple websites simultaneously.
Depending on the required level of trust, cost, and system scale, an appropriate certificate type can be selected. For individuals or small projects, a free DV certificate from Let’s Encrypt is usually sufficient, while businesses should consider OV or EV certificates to enhance credibility.
4. Differences Between SSL and TLS
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are both designed with the same goal – to protect data during transmission between the client and the server. However, they differ in terms of security level, performance, and technical standards.
Historically, SSL was the first version, developed by Netscape in the 1990s, including SSL 2.0 and SSL 3.0. Although these versions laid the foundation for today’s security protocols, they were later found to have serious vulnerabilities such as the POODLE and BEAST attacks, and are therefore no longer recommended for use.
TLS was subsequently introduced as the successor to SSL, starting with TLS 1.0 and continuing through TLS 1.1, TLS 1.2, and the current standard, TLS 1.3 – defined in RFC 8446. TLS inherits the basic structure of SSL but has been redesigned to be more secure, more efficient, and more scalable.

Quick Comparison Table Between SSL and TLS
| Criteria | SSL | TLS |
|---|---|---|
| Versions | SSL 2.0 / 3.0 (obsolete) | TLS 1.0 → 1.2 → 1.3 (current) |
| Security | Many vulnerabilities, easily exploited | Strongly improved encryption and better protection against spoofing |
| Performance | Slower, requires multiple handshake rounds | More optimized, especially TLS 1.3 with reduced connection latency |
| Recommended usage | Not recommended | TLS 1.2 or 1.3 is the current required standard |
In summary, TLS is essentially the “newer and more secure version of SSL.” When configuring a server, older versions such as SSLv3, TLS 1.0, or TLS 1.1 should be disabled, and only TLS 1.2 and TLS 1.3 should be enabled to ensure an optimal level of security for the system.
5. The Role and Importance of SSL/TLS in Information Security
SSL/TLS is not merely a technical tool – it is a core protective layer of the modern Internet, helping to maintain security, trust, and privacy in all online communications. Without SSL/TLS, any information you send or receive – such as passwords, bank card numbers, or personal data – could be intercepted or altered during transmission.

Specifically, SSL/TLS helps protect systems and users from the following risks::
- Man-in-the-Middle (MITM):
This is a type of attack in which a malicious actor intercepts communication between the client and the server, reading or modifying data without the user’s knowledge. When SSL/TLS is properly configured and valid certificates are used, all data is encrypted and authenticated, making it impossible for attackers to decrypt or tamper with the information. - Eavesdropping:
Data is encrypted using strong algorithms (such as AES or ChaCha20), so even if it is intercepted, the information appears as “meaningless strings of characters” to attackers. - Impersonation:
SSL/TLS uses digital certificates issued by a Certificate Authority (CA), allowing browsers to authenticate the server’s identity. This prevents users from being tricked into accessing fake websites that closely mimic legitimate ones.
In addition to these direct security benefits, SSL/TLS also provides strategic value for websites:
- Increased user trust: The padlock icon in the address bar creates a sense of security, making users feel more confident when conducting transactions.
- Improved SEO: Google has confirmed that HTTPS is a ranking signal. Although it is not a major factor, it is sufficient to improve search rankings compared to standard HTTP websites.
In summary, SSL/TLS serves both as a protective barrier for data and as a tool to strengthen a website’s credibility. In an Internet landscape that is increasingly complex and full of threats, deploying HTTPS is no longer an option – it is a mandatory standard for all online systems.
6. Conclusion
After this exploration, it is clear that SSL/TLS is not merely a technical protocol but also the foundation of trust on the Internet. Thanks to it, all information exchanged between users and servers is encrypted, authenticated, and protected against threats such as eavesdropping and impersonation.
Today, deploying HTTPS has become almost a mandatory requirement – not only to ensure data security, but also to build website credibility, improve user experience, and even support SEO. Whether you are a developer, a system administrator, or simply someone interested in security, understanding how SSL/TLS works will help you evaluate and configure network environments with greater confidence.
By mastering these principles, each of us can contribute to making the Internet a safer and more trustworthy space – where information is protected and trust becomes a shared standard rather than just an option.
7. Reference
[1] E. Rescorla, SSL and TLS: Designing and Building Secure Systems, Addison-Wesley, 2001.
[2] Internet Engineering Task Force (IETF), “The Transport Layer Security (TLS) Protocol Version 1.3,” RFC 8446, Aug. 2018.
[3] Mozilla, “Mozilla SSL Configuration Generator,” [Online]. Available: https://ssl-config.mozilla.org/.
[4] Google Security Blog, “HTTPS as a Ranking Signal,” Aug. 2014. [Online]. Available: https://developers.google.com/search/blog/2014/08/https-as-ranking-signal.
[5] Cloudflare, “What is SSL/TLS Encryption?” [Online]. Available: https://www.cloudflare.com/learning/ssl/what-is-ssl/
