A proxy acts as a silent “agent,” enhancing your security, optimizing your online experience, and unlocking access to parts of the Internet that are otherwise restricted.
Information Security
Overview of Information Security: Technology, People, and the Latest Security Trends
Information security is not solely a matter of technology, but a combination of people, processes, and awareness. In the digital era, where data has become a valuable asset, understanding security principles, user behavior, and emerging trends such as Zero Trust and the use of AI in cybersecurity is critical to survival.
SSL/TLS and Their Core Role in Information Security on the Internet
SSL/TLS is not merely a technical protocol but also the foundation of trust on the Internet. Through it, all information exchanged between users and servers is encrypted, authenticated, and protected against threats such as eavesdropping and impersonation.
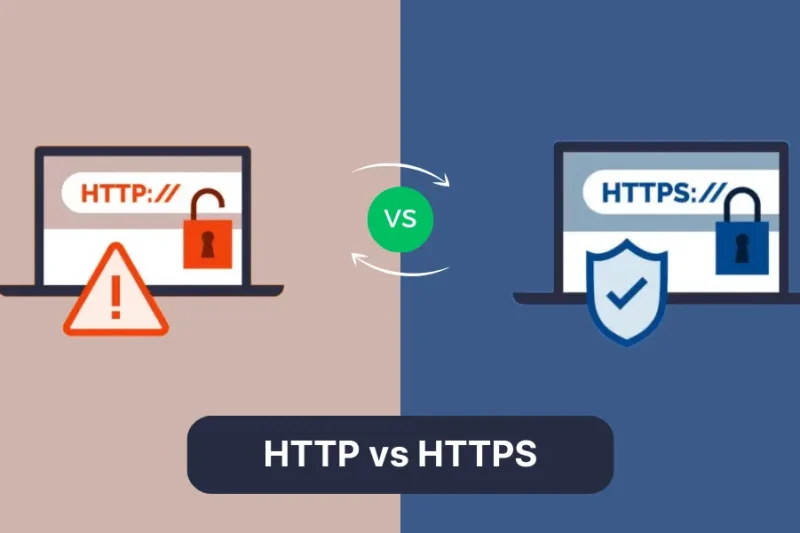
Understanding HTTP and HTTPS: Differences and Their Role in Website Security
When accessing a website, you often encounter two common protocols: HTTP and HTTPS. But how exactly do they differ? How does HTTP work, what makes HTTPS special, and why has security become such an important factor for websites today?
Understanding Phishing: Mechanisms, Impacts, and Security Measures
Phishing is a form of cyberattack that targets people, aiming to deceive users into providing sensitive information such as bank account details, passwords, credit card numbers, or other personal data.
Understanding Malware: Types, Impacts, and System Protection Methods
In the current digital era, malware – also known as malicious software – has become one of the most common and complex threats facing both individuals and organizations. Malware is capable of infiltrating computer systems, mobile devices, and even cloud platforms, thereby stealing data, disrupting operations, or causing serious financial losses.
Understanding Computer Viruses: Types, Operating Mechanisms, and Protection Measures
Computer viruses are malicious pieces of code capable of self-replication and spreading from one computer to another, often infiltrating systems silently without the user’s awareness. They can cause serious consequences, ranging from the loss of personal data and disruption of work to damaging network systems and inflicting financial losses on businesses.
What Is a Firewall? Understanding Its Principles, Types, and Applications in Network Security
A firewall is one of the most fundamental pillars of modern cybersecurity, enabling access control, network segmentation, and the logging of activities for monitoring and incident investigation purposes. However, a firewall alone is not a comprehensive shield capable of protecting an entire system.
What is a VPN? Understanding VPN: A Security and Privacy Tool in the Digital Age
A VPN (Virtual Private Network) was created as a solution that both protects personal information and provides the freedom to access content on the internet. VPN is no longer an unfamiliar concept, but many people still do not fully understand how it works, its benefits, and the risks of using it.
OWASP is what? Learn about OWASP and the Top 10 most common security vulnerabilities.
Learn what OWASP is, its role in web application security, and explore the Top 10 most common security vulnerabilities that developers need to master.